It’s 8:00 on a Sunday night and you’ve just finished reading our post on APT35 and AQUATIC PANDA, describing how these threat actors are actively exploiting the Log4j vulnerability. If only you could close all vulnerabilities, right? After all, regardless of your role (e.g., SOC, CTI, IR, management), you've spent the bulk of your career dealing with vulnerabilities in some way.
Like a continual game of whack-a-mole, much of our current security and compliance practice focuses on addressing vulnerabilities. To give some perspective, the Center for Internet Security’s 18 CIS Critical Security Controls (some of the most pragmatic security guidance available) refer to vulnerabilities three times as often as threats.
It’s time to end the game. Doing so requires that you shift to a threat-informed defense (TiD). A TiD applies a deep understanding of adversary tactics, techniques, and procedures (TTPs) to protect against and mitigate threats. The good news is relief is only three steps away. The bad news is you’re still facing a wall of vulnerabilities.
How is this working for you?
As you know, it is impossible to shut down all vulnerabilities which are endemic within IT. Just look at the OWASP Top 10: most of the same software vulnerabilities continue to make the list year after year. And as discussed in our previous blog, “Operationalize Your Threat Intelligence in Four Moves,” the expanding attack surface (i.e., mobile, cloud, work-from-home, and Internet of Things) increases the potential for vulnerabilities across the enterprise.
Are vulnerabilities and threats two sides of the same coin?
From working with some of the most targeted organizations in the world, we believe that vulnerabilities and threats are two sides of the same coin. But the relationship is not a simple one. There are two issues. First, given the overwhelming number of active vulnerabilities, implementing a patching/mitigation strategy without considering the threat side of the equation is a waste of resources. There is no way that you can address all vulnerabilities, so without considering the threat, you have no way to prioritize your response. Worse, you may feel good that you're meeting your patching metrics (e.g., percentage of systems patched, time to patch), but you’re most likely leaving vulnerabilities open to active threat exploit. It only takes one unpatched Apache Struts server to lead to an Equifax breach.
The second issue is possibly the more difficult one. Even if you could have a "perfect-image" infrastructure with no known vulnerabilities, it would still be vulnerable to most threat actor tactics, techniques, and procedures (TTPs). Yes, this is a harsh reality, but as the Lockheed Martin Kill ChainTM shows us, after the initial exploit, most threat activity is independent of vulnerabilities in your infrastructure.
Bottom line: you cannot address vulnerabilities effectively without also addressing the threat-vulnerability relationship.
What can you do?
We recommend shifting from a vulnerability/compliance to a threat-centric mindset by adopting a threat-informed defense (TiD) approach.
Initially developed by MITRE, a "threat-informed defense applies a deep understanding of adversary tradecraft and technology to protect against, detect, and mitigate cyber-attacks." As MITRE goes on to state, "it's a community-based approach to a worldwide challenge."1
Keep in mind that a TiD is not a tool or a specific tactic. It's a methodology with three components:
1) Understanding your adversaries and their TTPs
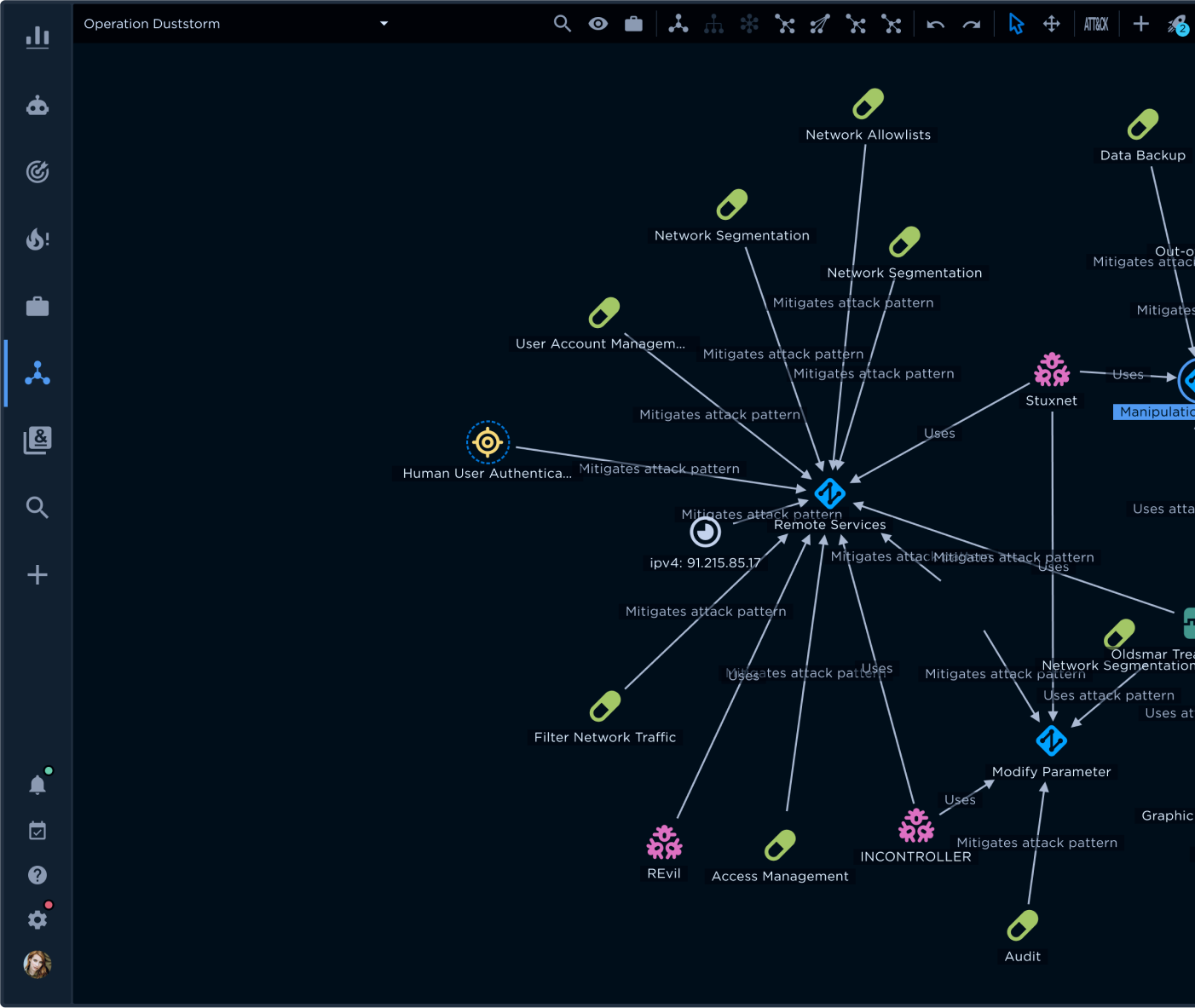
The heart of any TiD is MITRE ATT&CK®, a curated knowledge base and model for cyber adversary behavior. ATT&CK provides a common language to align threat information, vulnerabilities, capabilities, mitigations, and controls.
2) Determining your crown jewels, their location, and your ability to defend them
- Identifying the most valuable assets in your organization is a foundational step for risk management. Many organizations either skip over this step as they race to shut down vulnerabilities, or they do not continually update their inventories, particularly as assets move to the cloud.
- The second part of this component is assessing your ability to defend your assets, leading right into the third component.
3) Implementing a security effectiveness program by instituting best practices to align red and blue teams, or better yet, establish a purple team.
Most organizations lack the resources for formal blue and red teams, and those that do often slip into competitive and uncooperative practices. A purple team puts everyone on the same team while still testing your ability to defend against threats.
Do I need to stop worrying about vulnerabilities?
One benefit of using a TiD is putting your vulnerabilities into perspective. As Rich Struse, co-founder of the Center for Threat-Informed Defense at MITRE says, "threat-informed defense includes other threat information, such as vulnerabilities and open source and closed source intelligence. It includes defensive context, such as capabilities, mitigations, and controls."2
Be aware. Adopting a TiD requires you to shift the way you think about security and risk management. You may currently be facing tens of thousands of vulnerabilities in your environment. By turning to the threat side of the coin, you are looking at several hundred techniques a threat actor may employ. In our post “Shifting from What to How with TTPs,” when we talk about the pyramid of pain, we explain why there is such a huge numbers gap between vulnerabilities and techniques.
By shifting your emphasis from vulnerabilities to threats with TiD, you eliminate vulnerability whack-a-mole by using threat information to prioritize your vulnerability management.
Adopting the TiD approach sets you up to focus on the threats that matter most. You still worry about vulnerabilities, but it allows you to prioritize what vulnerabilities you close first.

How do I implement a threat-informed defense?
We recommend the following steps to get started on your TiD journey:
1) Shift your focus to the threat side of the coin.
This shift includes identifying the most likely threats your organization will encounter. There are many sources (open and commercial) of relevant threat intelligence, but an information sharing and analysis center (ISAC) aligned to your specific vertical is a great place to start. For a complete list, please check out https://www.nationalisacs.org/member-isacs-3.
2) Assess your crown jewels and their location.
Look at the potential impact of a compromise in confidentiality, integrity, or availability (CIA) of each asset. Adversaries have different goals, but fundamentally, they all target one or more of the CIA triad.
3) Optimize your security approach by qualifying and, if possible, quantifying the risks associated with the threats.
This step builds on a clear assessment of your crown jewels and requires a deep understanding of the effectiveness of your controls. With this information, you can prioritize your investments in your controls.
Summary benefits of a TiD
So, what are the benefits of a TiD? We see four primary advantages that align well with the benefits of putting Intelligence at the CoreTM, our mantra. First, implementing a TiD helps you close coverage gaps from siloed operations and an over-emphasis on security point solutions. Specifically, simulating and emulating adversary attacks against your infrastructure expose gaps and weaknesses in coverage. Second, implementing MITRE ATT&CK® empowers your defenders to better track TTPs, identify attacks against your environment, and determine your most critical vulnerabilities that require immediate attention. Third, following a TiD helps with your detection by leveraging human intelligence. The heart of MITRE ATT&CK® is intelligence that is crowdsourced by a global community of intelligence analysts and practitioners. Finally, aligning with MITRE ATT&CK® improves collaboration by creating a common language and taxonomy to discuss active threats.
To learn how you can use MITRE ATT&CK® to track adversary TTPs, please read our post “How to Use MITRE ATT&CK to Map and Track Adversary TTPs.”