It's time to be resilient, not just secure
The days of putting all your cyber resources into prevention are over. The expanding attack surface, driven by digital transformation, and accelerated by work from home (WFH), provides an increasingly target-rich environment. It's no longer a question of if, but rather when an adversary will breach your organization's defenses. That's why it's time to shift your focus from cyber security to cyber resilience.
As the World Economic Forum defines it, cyber resilience is the "the ability of an organization to transcend (anticipate, withstand, recover from, and adapt to) any stresses, failures, hazards and threats to its cyber resources within the organization and its ecosystem, such that the organization can confidently pursue its mission, enable its culture and maintain its desired way of operating."1
Becoming cyber resilient is a big move that involves the entire organization. For most organizations, it's a multi-year journey. The great news is that you and your CTI team can get the cyber resilience train moving today by focusing on the first step: anticipating threats.
Early warning empowers cyber resilience
The earlier you can anticipate an attack, the better you can transcend the attack and any resulting impacts. Anticipation depends on an early warning.
Early warning involves processing threat intelligence from trusted sources to establish alerts in time to take the necessary steps to improve cyber resilience. According to an EclecticIQ financial services client, his team achieves early warning "by looking over the horizon." The team creates this over-the-horizon view by establishing threat information sharing arrangements with peer financial services organizations and the financial services information sharing and analysis center (FS-ISAC), supported by a threat intelligence management platform that facilitates the collection, analysis, and production of threat intelligence to support multiple risk, security, and response teams at the bank.
So, how do you achieve early warning for your organization?
Early warning starts with effective threat intelligence sharing and collaboration
Central to our client's early warning process is threat intelligence sharing with other financial services organizations. This process requires tight cooperation among entities, both public and private. These public/private collaborative efforts are increasingly seen by cyber leaders as a "key to ensuring national cyber resilience."2 In some cases, threat intelligence sharing is voluntary, although regulations (e.g., Europe's NIS2 Directive) are increasingly pushing organizations to share this information.
Public/private interaction is a core aspect of threat sharing. For example, government agencies are responsible for protecting critical infrastructure. However, across much of the world, most critical infrastructure resources (e.g., telecom, power, health care, water) are primarily owned or operated by private companies. A government agency can only meet its national security needs of protecting critical infrastructure through public-private cooperation.
Becoming your own NCSC or ISAC
Cooperative sharing is not just the domain of governments and global banks. Cyber resilience requires all organizations, public and private, to cooperate across the supply chain. To underscore this point, the World Economic Forum found that "Almost 40% of respondents have been negatively affected by a third-party vendor/supply chain organization cybersecurity incident. Nearly half (44%) of the surveyed CEOs indicated that software supply chain attacks will have the greatest influence on their organization's approach to cybersecurity in the future."3
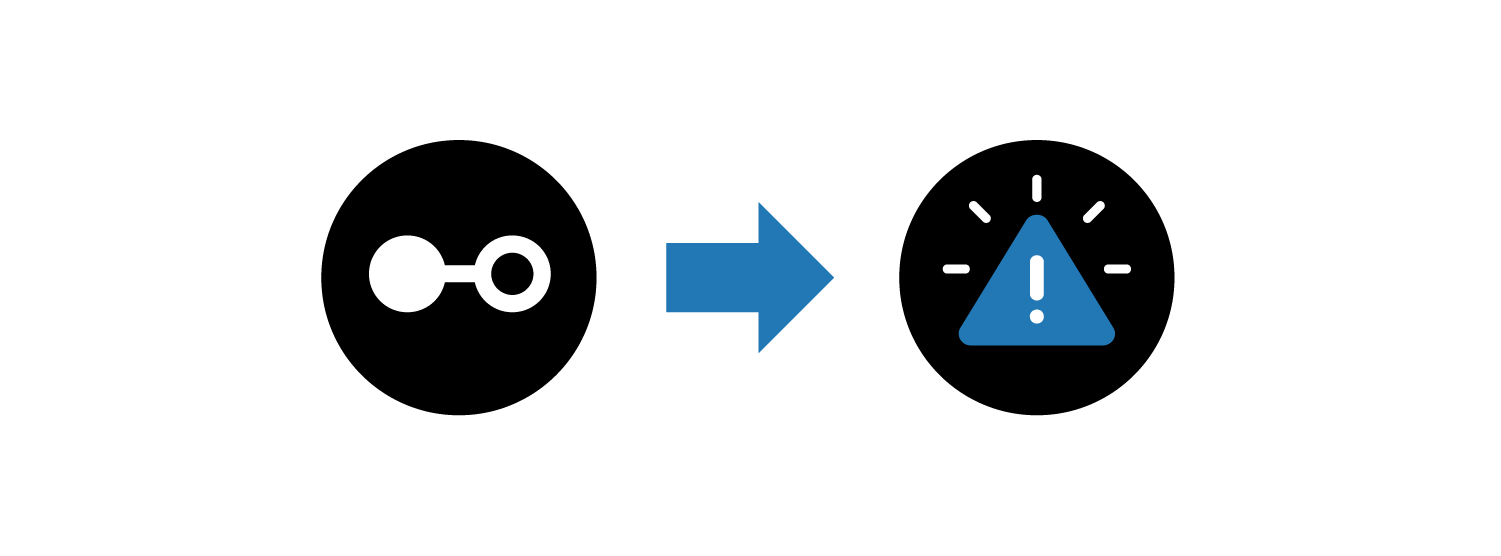
One supplier breach can take down your organization and many others in your industry at the same time. For example, in 2021, the REvil ransomware group exploited a remote monitoring and management software platform vulnerability, disrupting 1,500+ companies worldwide. Particularly hard hit was a Swedish grocery chain, which temporarily closed more than 800 stores.
Your dependence on the supply chain means your attack surface no longer ends at your corporate data center. For this reason, you must act more like a national cyber security center (NCSC) or ISAC to provide early warning for your supply chain.
Cyber resilience, NCSCs, and ISACs
Indeed, cyber resilience is already a central theme for major threat sharing organizations. National cyber security centers and ISACs make cyber resilience part of their mission. As the UK NCSC states in its 2021 annual report, "One of the NCSC's most important priorities this year was to increase the resilience of the UK against cyber threats and strengthening the systems pivotal to the nation's response to Covid-19."4 Similarly, the financial services ISAC's mission is to "help assure the resilience and continuity of the global financial services infrastructure and individual firms against intentional acts that could significantly impact the sector's ability to provide services critical to the orderly functioning of the global economy."5
Sharing is caring but not sufficient for early warning
Establishing early warning is easier said than done. Unfortunately, threat intelligence that organizations share is often irrelevant and, worse, a huge distraction.
Three things determine the usefulness of shared threat intelligence: being reliable, easy to consume, and actionable. Why these three? Unreliable intelligence is the cyber equivalent of crying wolf. Very quickly, organizations turn off unreliable threat intelligence feeds. When the threat intelligence is reliable but not actionable, it raises the alarm – correctly – but it doesn't help address the threat. A CTI director at a global financial services firm (and a customer of EclecticIQ) continually reminds his team that actionable intelligence clearly defines not just the threat but also its impact and likelihood. Too often, threat intelligence only focuses on the threat and loses sight of the impact and likelihood. Finally, even when threat intelligence is reliable and actionable, it's worthless to the intended party if it isn't consumable. For example, it won't help your risk manager to receive a detailed threat analysis with MITRE ATT&CK® techniques and suggested mitigations from your analyst. Similarly, mapping threats, impacts, and the expected loss against the corporate risk appetite is worthless to your SOC team when trying to block an active attack.
Two examples of early warning for cyber resilience
For examples of threat sharing that contribute to effective early warning, we look to a public and a private organization. In both cases, we focus on the threats associated with the COVID-19 pandemic.
The first example comes from the UK NCSC. The NCSC recognized that the pandemic had created new areas of vulnerability, particularly in vaccine and health sector supply chains. To address this, the UK NCSC engaged international partners in 13 countries and the World Health Organization (WHO) to help secure the overseas supply chains for vaccines and to enhance partners' resilience against cyber adversaries targeting those supply chains.
This collaboration and sharing provided early warning for participants by sharing critical intelligence about active and impending attacks against the vaccine supply chain. As the UK NCSC stated, this collaborative effort "provided immediate security benefits to the UK's vaccine and health sector supply chains and yielded longer-term benefits for bolstering the UK's international security."6
The second example comes from the EclecticIQ Threat Research Team. During its ongoing COVID-19 analysis, the team analyzed derivative vaccine developer domains (e.g., bigvacs.com vs. bogvacs.com vs. bigvax.com) from the WHO vaccine developers list for any known malicious activity. This approach created reliable threat intelligence.
This research led the team to alert a major vaccine developer with confirmation that an unrelated entity had registered infrastructure that was very likely spoofing the infrastructure of a vaccine researcher at the company. Also, the potential threat actor had active email services set up and configured in a way that raised suspicions of possible spear phishing intent. These findings and insights made the threat intelligence actionable, providing clear direction to detect and prevent an active threat vector.
EclecticIQ worked through the appropriate secure channels to alert on the threat, and the company reportedly acted appropriately. For ongoing analysis, the team uploaded the IOCs into EclecticIQ Intelligence Center and continued monitoring for any other related intelligence connected to those IOCs. This approach made the threat intelligence consumable by the vaccine manufacturer and any associated organizations using EclecticIQ Intelligence Center and EclecticIQ Curated Feeds.
This second example shows how using reliable, consumable, and actionable threat intelligence to provide early warning ultimately helped a vaccine manufacturer increase its cyber resilience.
Next steps
The beauty of establishing threat sharing and collaboration for early warning is that you can do it today. It does not require re-architecting your security plan to develop cyber resilience. As discussed in our next post, we outline three steps that you can take to implement collaboration and sharing to produce reliable, consumable, and actionable CTI to support cyber resilience by establishing early warning.
Footnotes
- "Global Cybersecurity Outlook 2022," World Economic Forum, 2022 Page 15
- "Global Cybersecurity Outlook 2022," World Economic Forum, 2022 Page 23
- "Global Cybersecurity Outlook 2022," World Economic Forum, 2022. Page 25
- “Annual Review 2021: Making the UK the safest place to live and work online,” National Cyber Security Centre, 2021. Page 34
- “Annual Review 2021: Making the UK the safest place to live and work online,” National Cyber Security Centre, 2021. Page 83